Database of Phone Hackers Websites: Understanding the Risks and Consequences
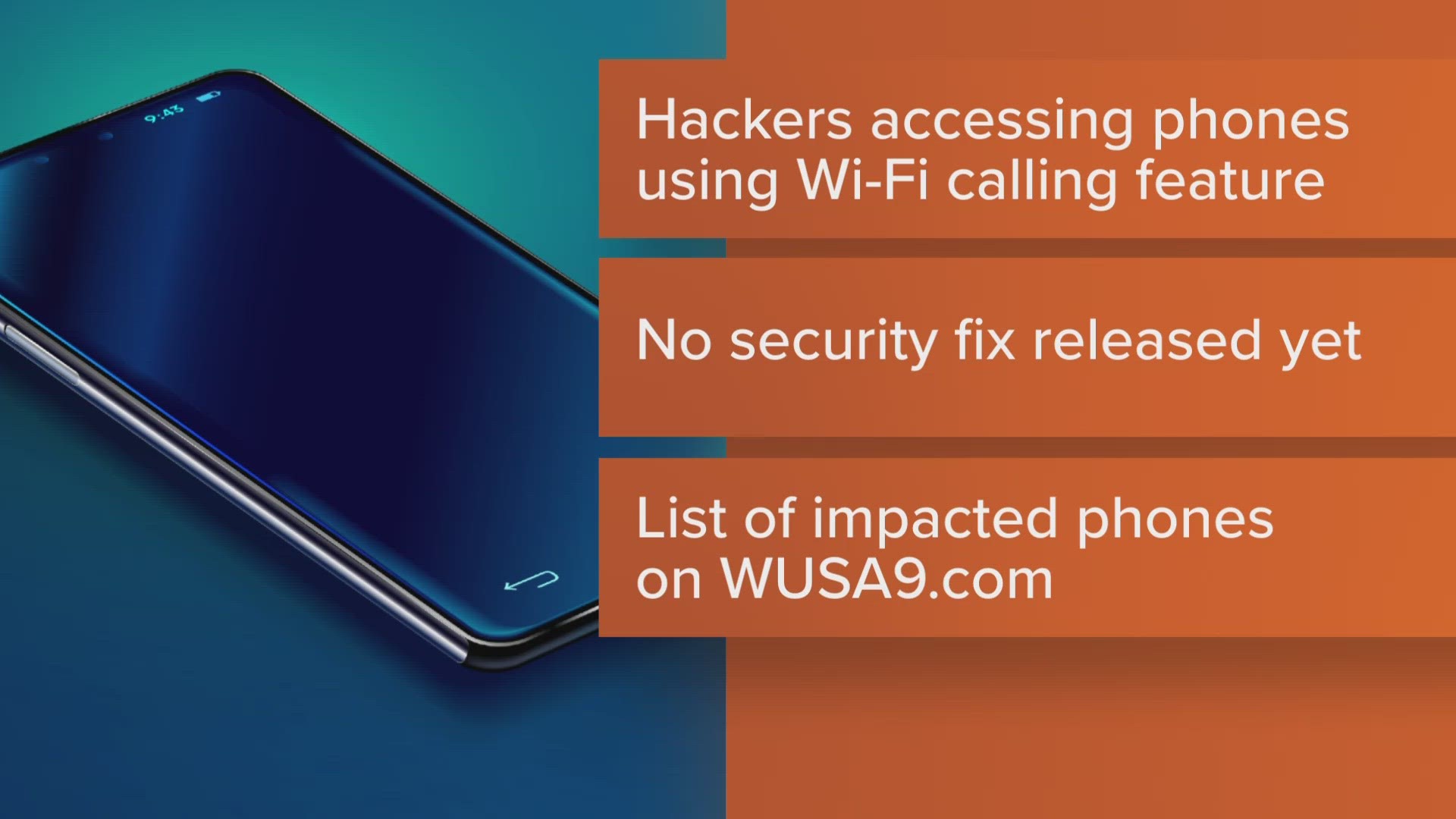
With the rise of digital transactions and online transactions, the risk of phone hacking has increased significantly. Malicious hackers are using various techniques to compromise phone numbers, including creating websites that can install malware or spyware on unsuspecting users' devices. To stay ahead of these threats, it's essential to have access to a database of phone hackers websites. In this article, we will explore what these databases are, how they can help you protect yourself, and how to use them effectively.
What is a Database of Phone Hackers Websites?
A database of phone hackers websites is a collection of websites that have been identified as malicious or suspicious. These websites may be used to install malware or spyware on users' devices, steal personal information, or engage in other nefarious activities. Having access to such a database can help you identify potential threats and take steps to protect yourself.

Why Do You Need a Database of Phone Hackers Websites?
There are several reasons why you need a database of phone hackers websites. Firstly, it can help you protect yourself from potential threats. By knowing which websites are malicious, you can steer clear of them and avoid installing malware or spyware on your device. Secondly, a database of phone hackers websites can help you detect potential threats before they become actual threats. Finally, having access to such a database can help you take proactive measures to protect your personal information and prevent identity theft.
How Do You Access a Database of Phone Hackers Websites?

There are several ways to access a database of phone hackers websites. You can start by searching online for reputable sources that provide such databases. Some popular sources include BreachDatabase.net, which provides access to a secure database of leaked credentials and compromised data. Another resource is HadIBeenPwned, which allows you to check whether your email address has been exposed in a data breach. You can also use a data breach search engine like HackCheck to safeguard your valuable data from data breaches.
When searching for a database of phone hackers websites, there are several key features to look for. Firstly, consider the credibility and reputation of the source. Look for sources that have been around for a while and have a good track record of accuracy. Secondly, consider the type of information provided. A good database should provide detailed information on the websites, including their IP addresses, domain names, and any other relevant details. Finally, consider the ease of use and navigation of the database. A good database should be easy to search and navigate, making it easy for you to identify potential threats and take action.
Best Practices for Using a Database of Phone Hackers Websites

As we can see from the illustration, Database Of Phone Hackers Websites has many fascinating aspects to explore.
When using a database of phone hackers websites, there are several best practices to keep in mind. Firstly, always verify the credibility of the source before using it. Secondly, be cautious when searching for potential threats, as some websites may be listed in error. Finally, take action promptly if you identify a potential threat. This may involve reporting the website to the relevant authorities or taking steps to protect your personal information.
Conclusion
Having access to a database of phone hackers websites can help you protect yourself from potential threats and take proactive measures to protect your personal information. By understanding the risks and consequences of phone hacking, you can stay ahead of these threats and keep your devices and data safe.
Resources
- BreachDatabase.net: A secure database of leaked credentials and compromised data.
- HadIBeenPwned: A service that allows you to check whether your email address has been exposed in a data breach.
- HackCheck: A data breach search engine that helps safeguard your valuable data from data breaches.
- CVEDetails.com: A vulnerability intelligence solution that provides CVE security vulnerability database, exploits, advisories, and product risk scores.
- TheHackerNews: A top cybersecurity news platform that delivers real-time updates, threat intelligence, data breach reports, and expert analysis.