Ways to Secure WiFi Network with Allowlisting
Securing your WiFi network is a crucial step in protecting your personal and business data from cyber threats. One effective way to achieve this is by implementing allowlisting, a security measure that only permits pre-approved devices to access your network. This article will explore the various ways to secure your WiFi network with allowlisting.
Understanding Allowlisting
Allowlisting, also known as whitelisting, is a cybersecurity strategy that only permits trusted devices, users, or applications to access your network. This approach is based on the principle of "known good" rather than "known bad," where only authorized entities are allowed to operate on your network. By implementing allowlisting, you can significantly reduce the risk of cyber threats and data breaches.
Types of Allowlisting

Such details provide a deeper understanding and appreciation for Ways To Secure Wifi Network With Allowlisting.
There are different types of allowlisting, including:
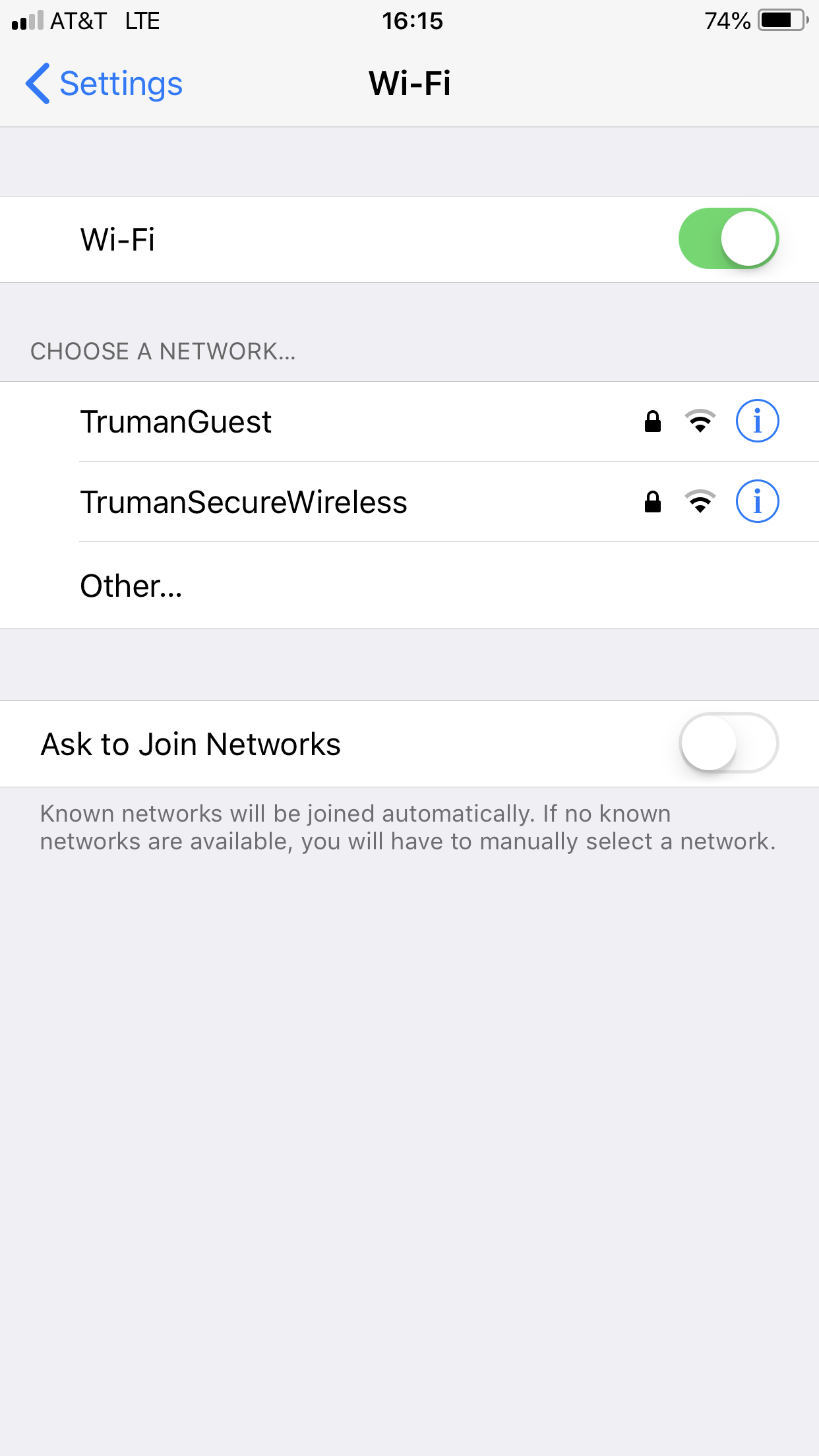
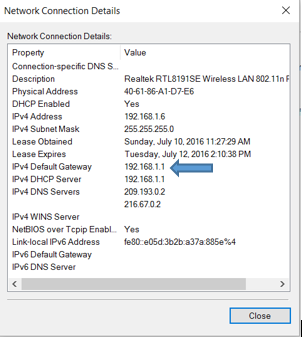
- MAC Address Allowlisting: This involves creating a list of permitted MAC addresses that can access your network.
- IP Allowlisting: This allows only pre-approved IP addresses to access your network.
- Application Allowlisting: This restricts access to only pre-approved applications or services.
- Network Access Control (NAC) Allowlisting: This is a more comprehensive approach that combines multiple security measures to control network access.
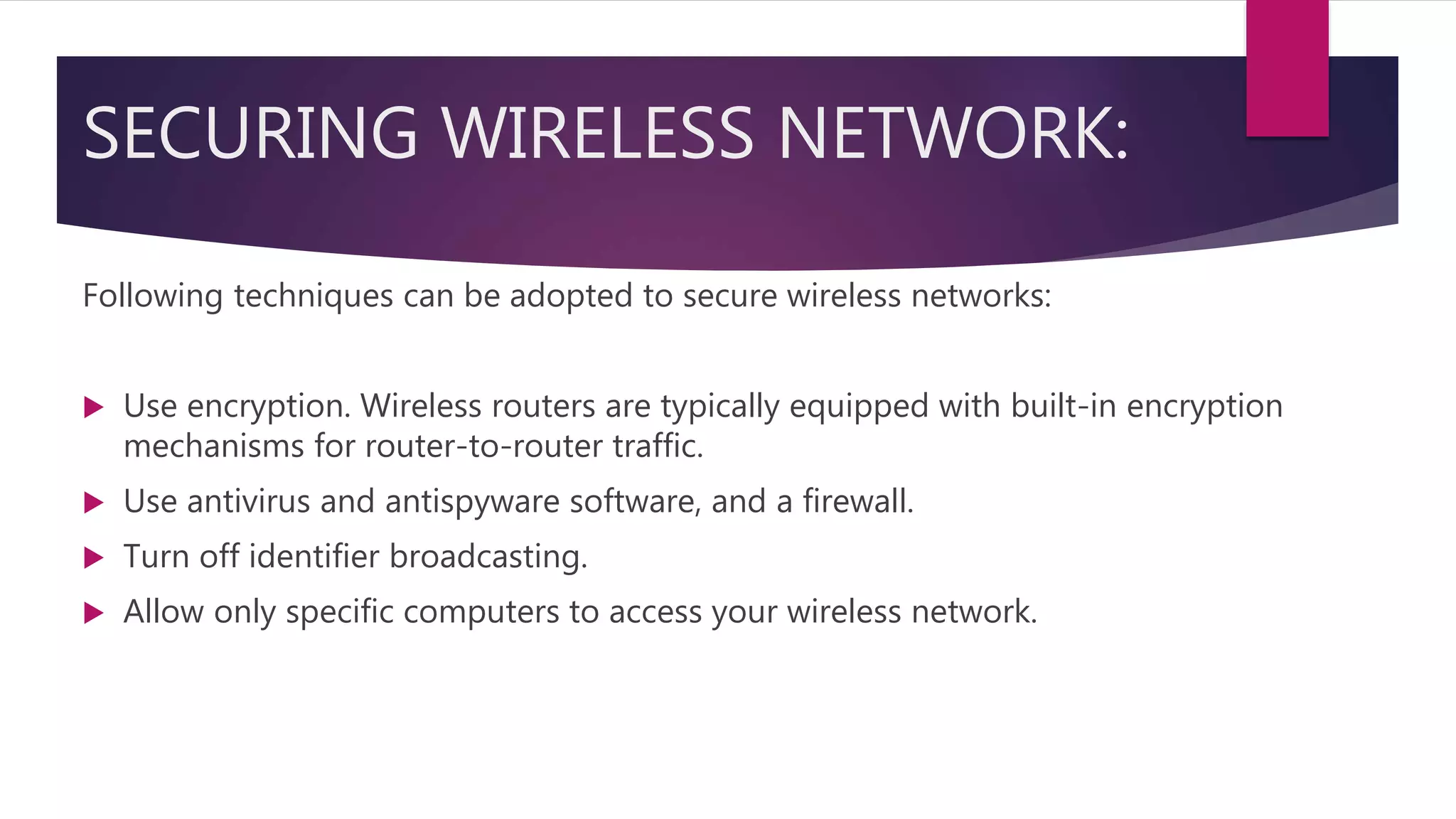
Best Practices for Implementing Allowlisting
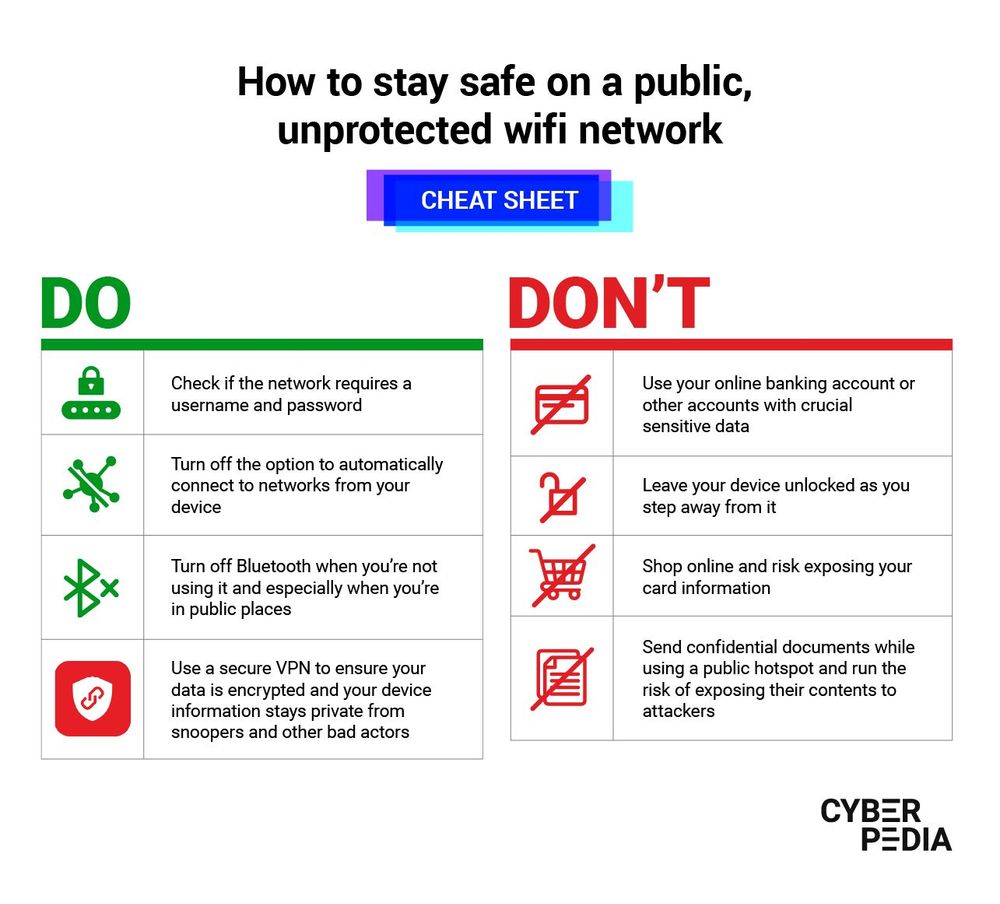
Here are some best practices for implementing allowlisting on your WiFi network:
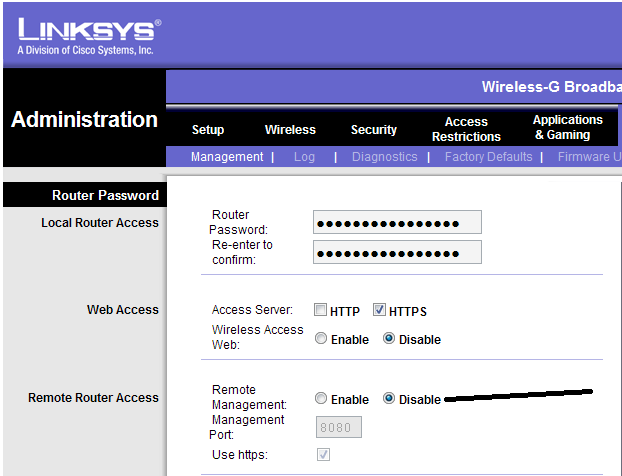
- Identify your network devices and create a list of authorized devices to include in your allowlist.
- Use a robust device management system to manage and update your allowlist.
- Regularly monitor your network activity to detect and prevent unauthorized access attempts.
- Keep your allowlist up-to-date by removing devices that are no longer authorized to access your network.
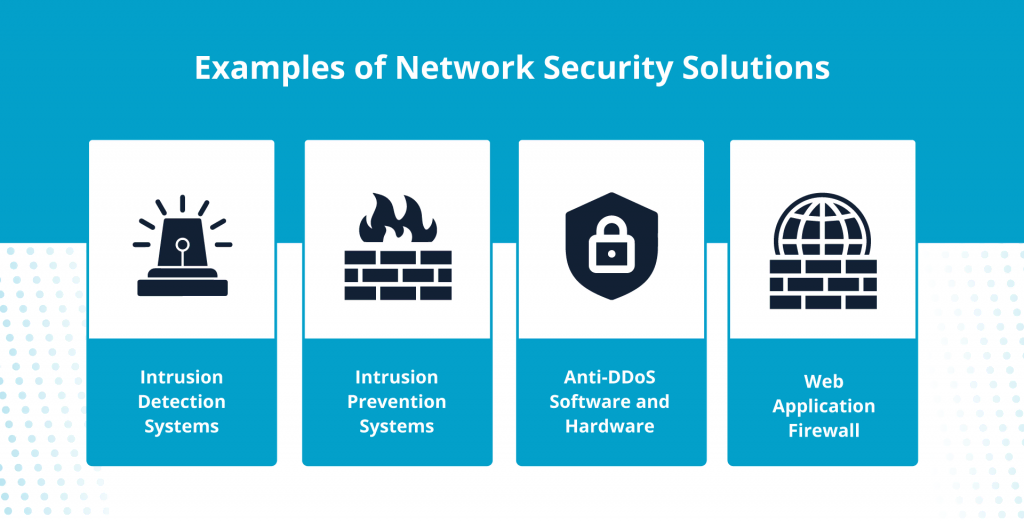
- Implement multiple layers of security, including firewalls, intrusion detection and prevention systems, and antivirus software.
Benefits of Allowlisting
Allowlisting offers several benefits, including:
- Improved network security by preventing unauthorized access.
- Reduced risk of data breaches and cyber threats.
- Enhanced compliance with regulatory requirements.
- Better control over network access and usage.

This particular example perfectly highlights why Ways To Secure Wifi Network With Allowlisting is so captivating.
Challenges and Considerations
- Complexity and difficulty in implementing and managing allowlists.
- Risk of false positives and false negatives.
- Need for regular updates and maintenance to keep your allowlist current.
Conclusion
Securing your WiFi network with allowlisting requires a comprehensive approach that involves identifying and managing authorized devices, implementing robust security measures, and regularly monitoring network activity. By following the best practices outlined in this article, you can effectively implement allowlisting and protect your network from cyber threats.







_20240830055723o.jpg)