Understanding G Network Configuration for Network Segmentation and Isolation
In today's complex networked world, ensuring the security and efficiency of your network is crucial. Network segmentation and isolation are two critical concepts that help achieve this goal. In this article, we'll explore the importance of G Network Configuration for Network Segmentation and Isolation, and discuss how it can be implemented.What is G Network Configuration for Network Segmentation and Isolation?

Such details provide a deeper understanding and appreciation for G Network Configuration For Network Segmentation And Isolation.
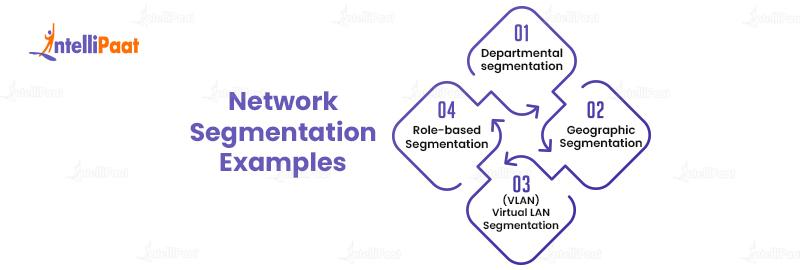
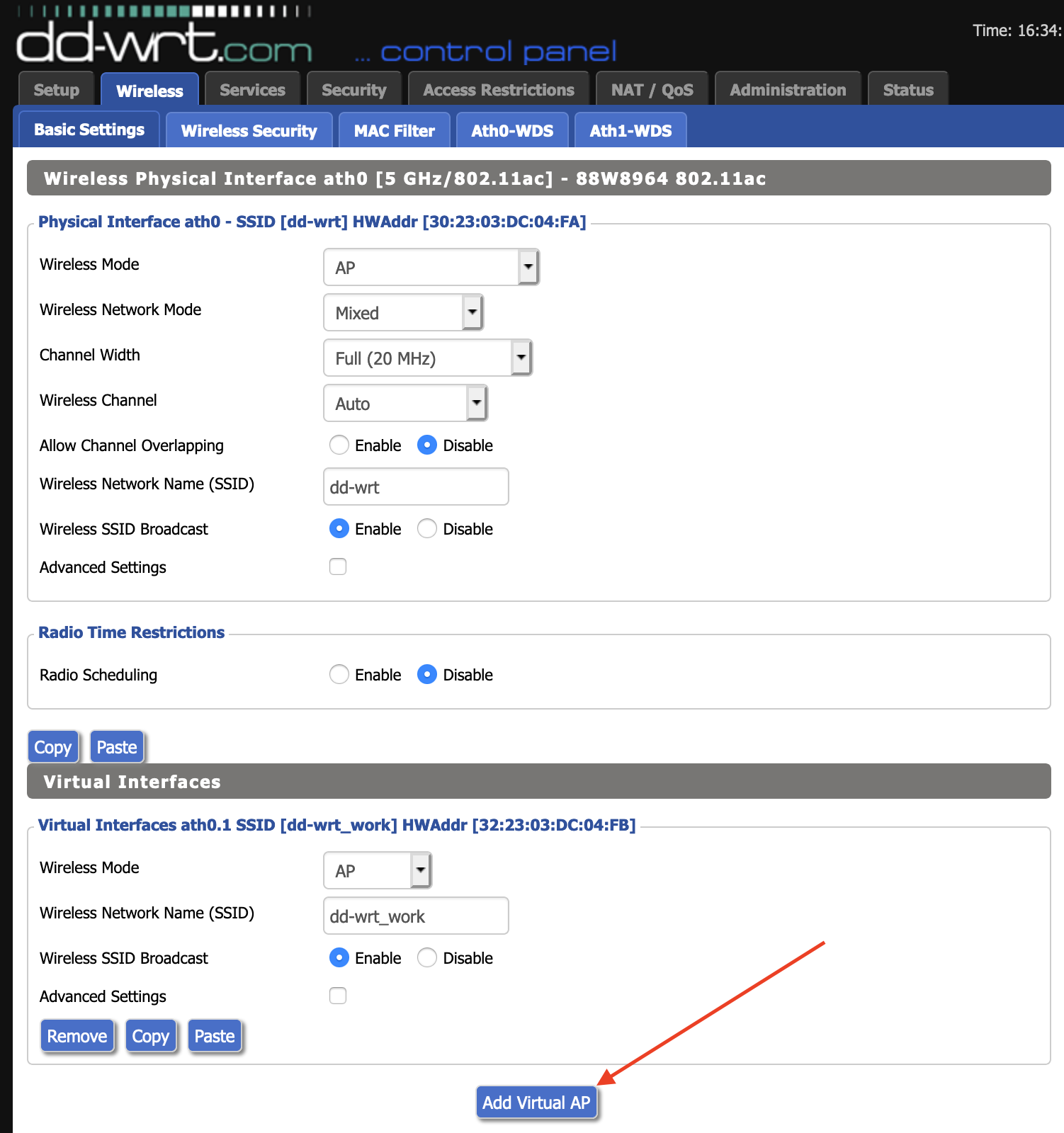
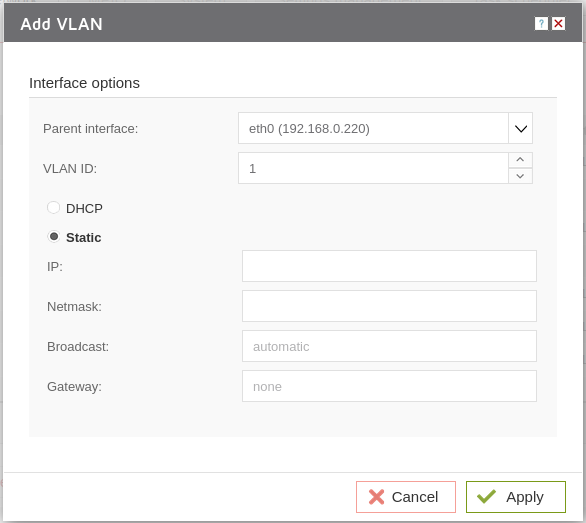
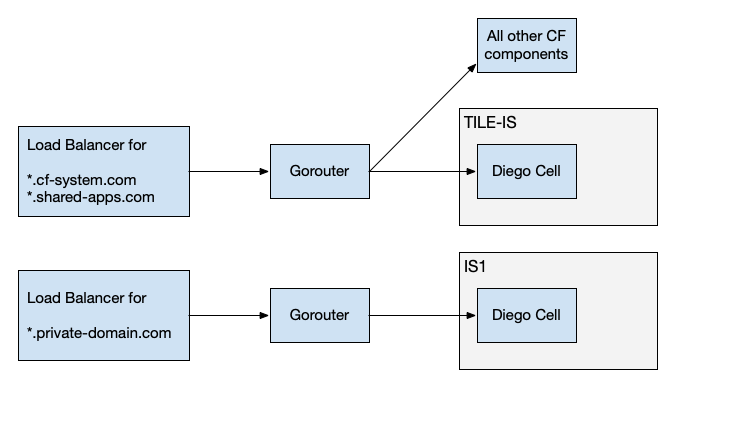
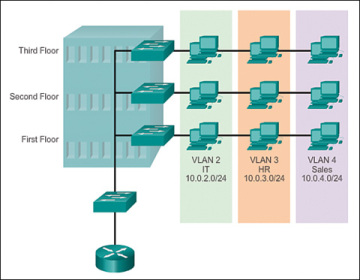
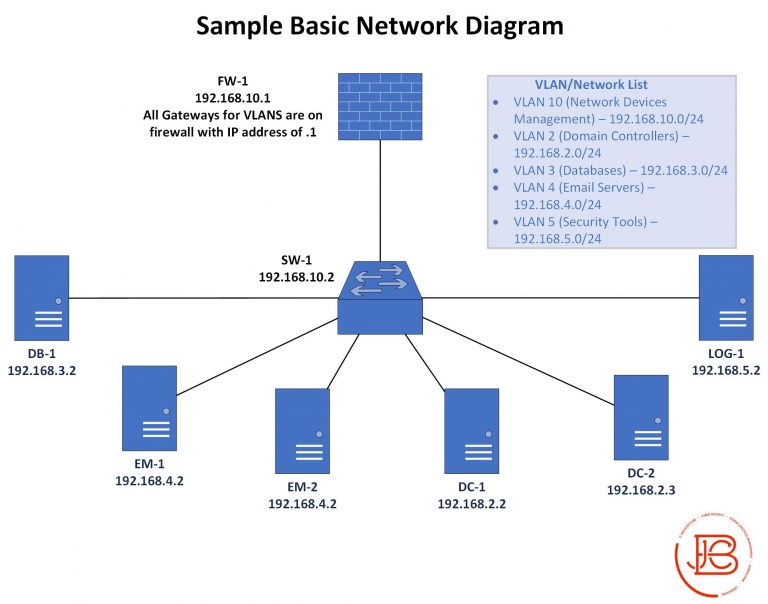
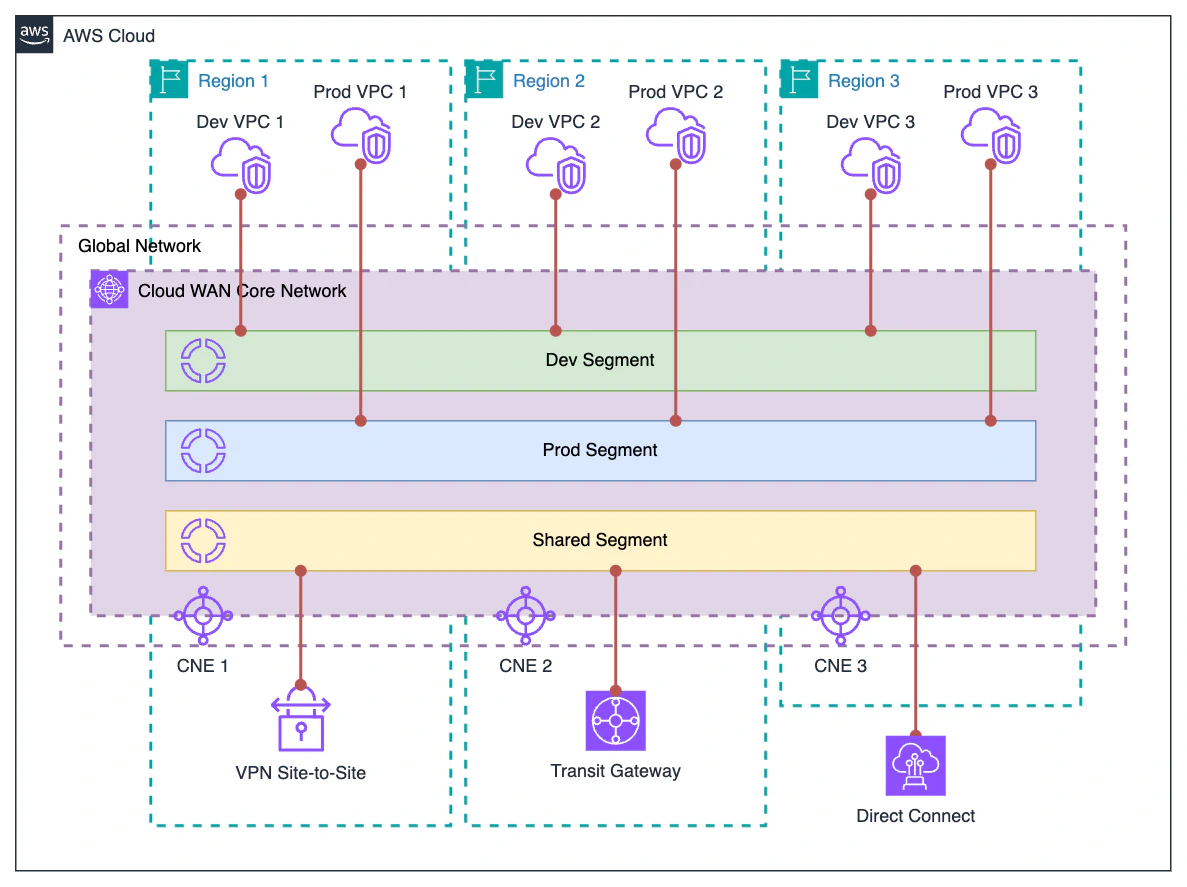
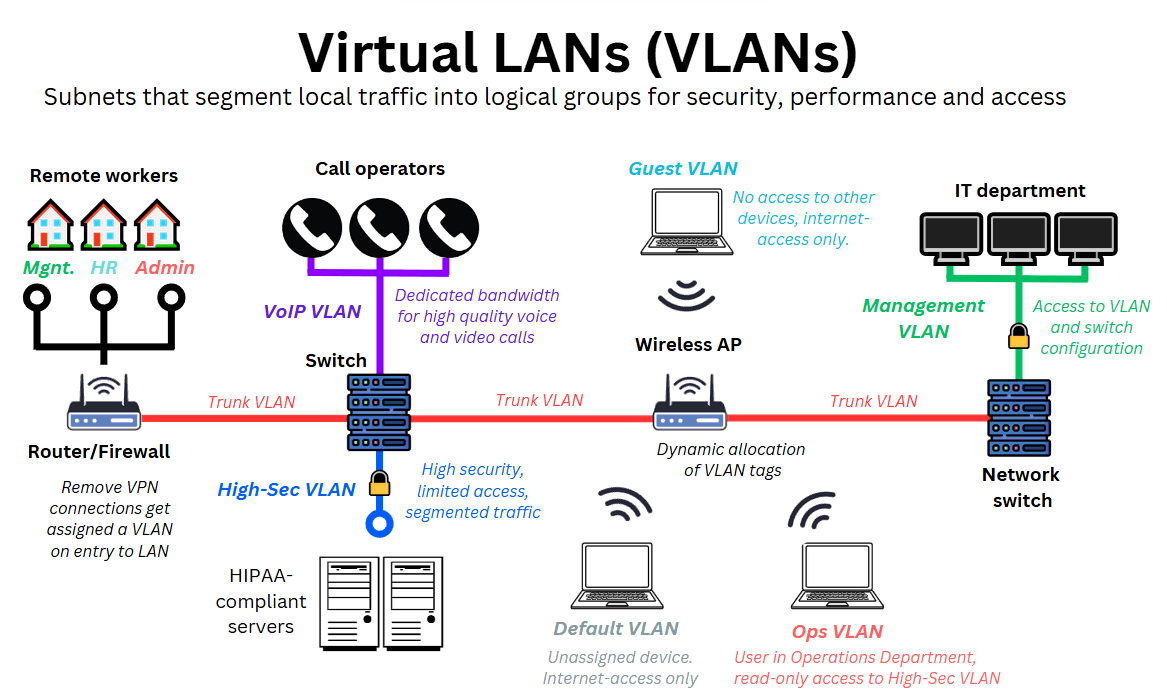
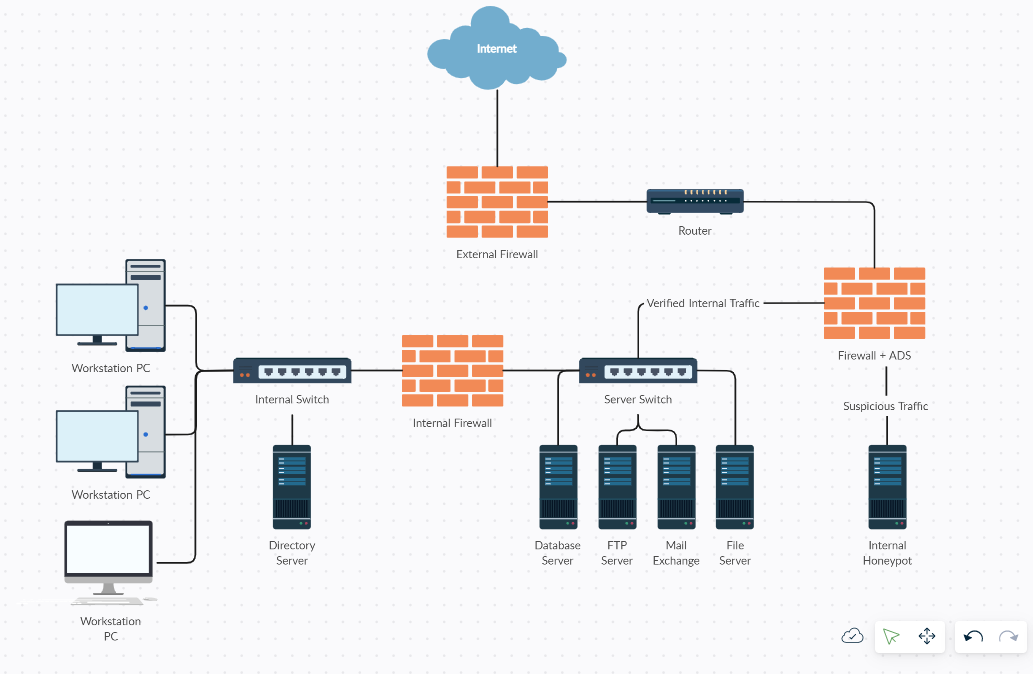
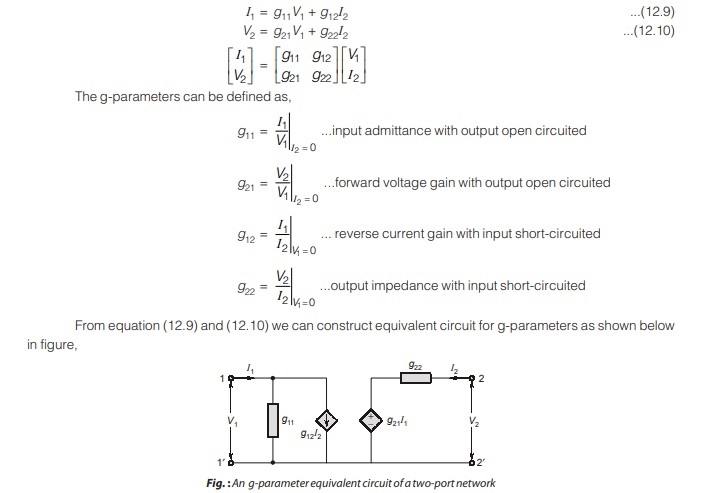
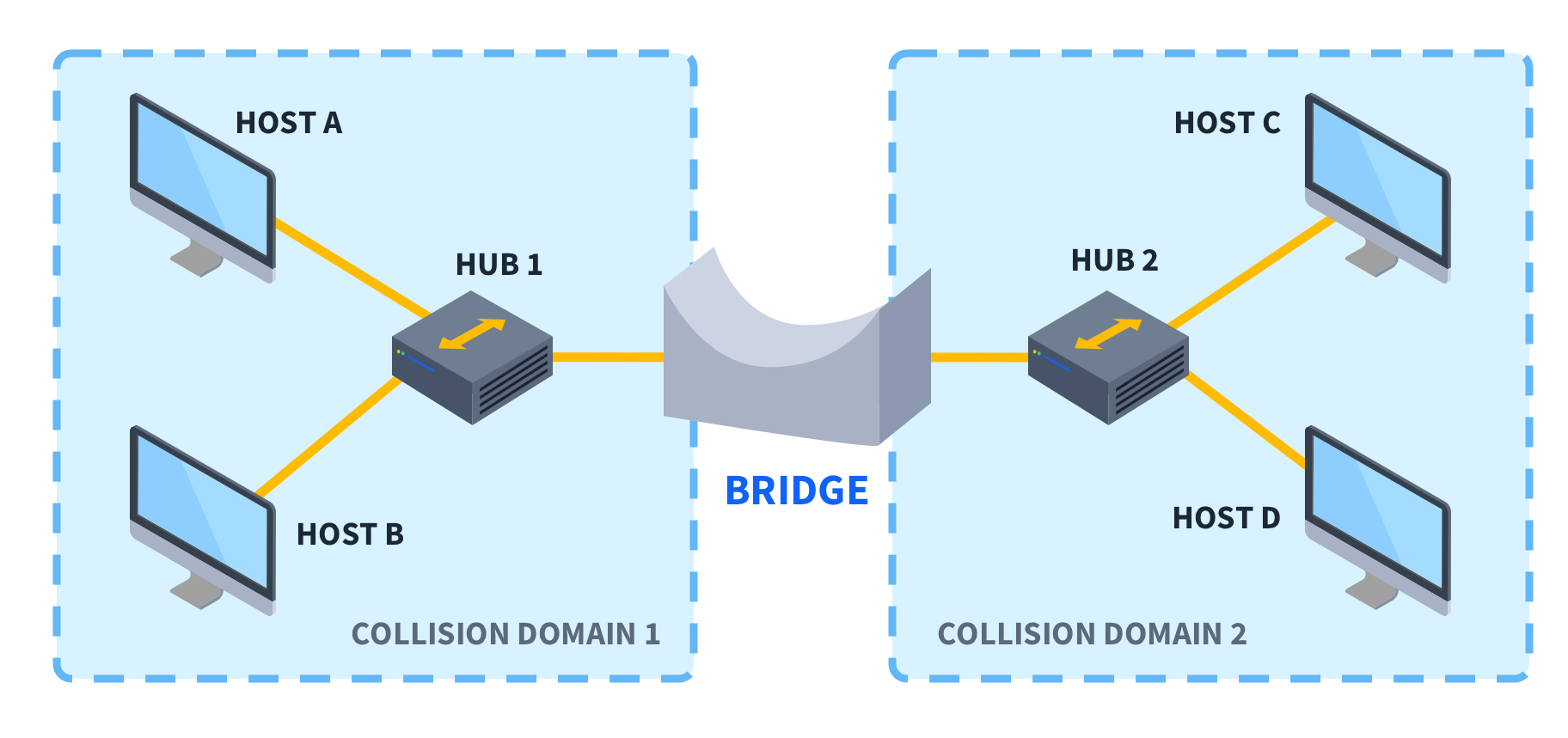
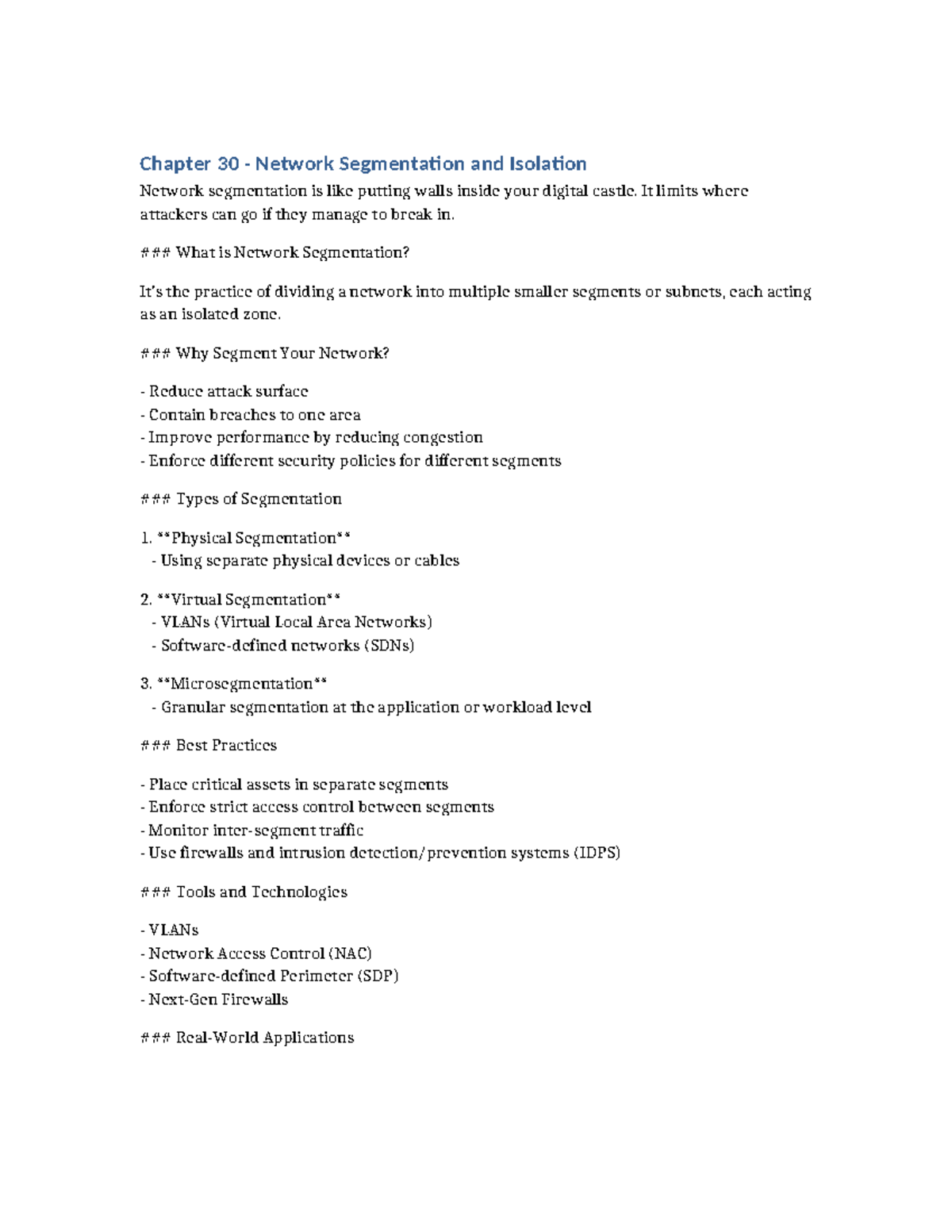
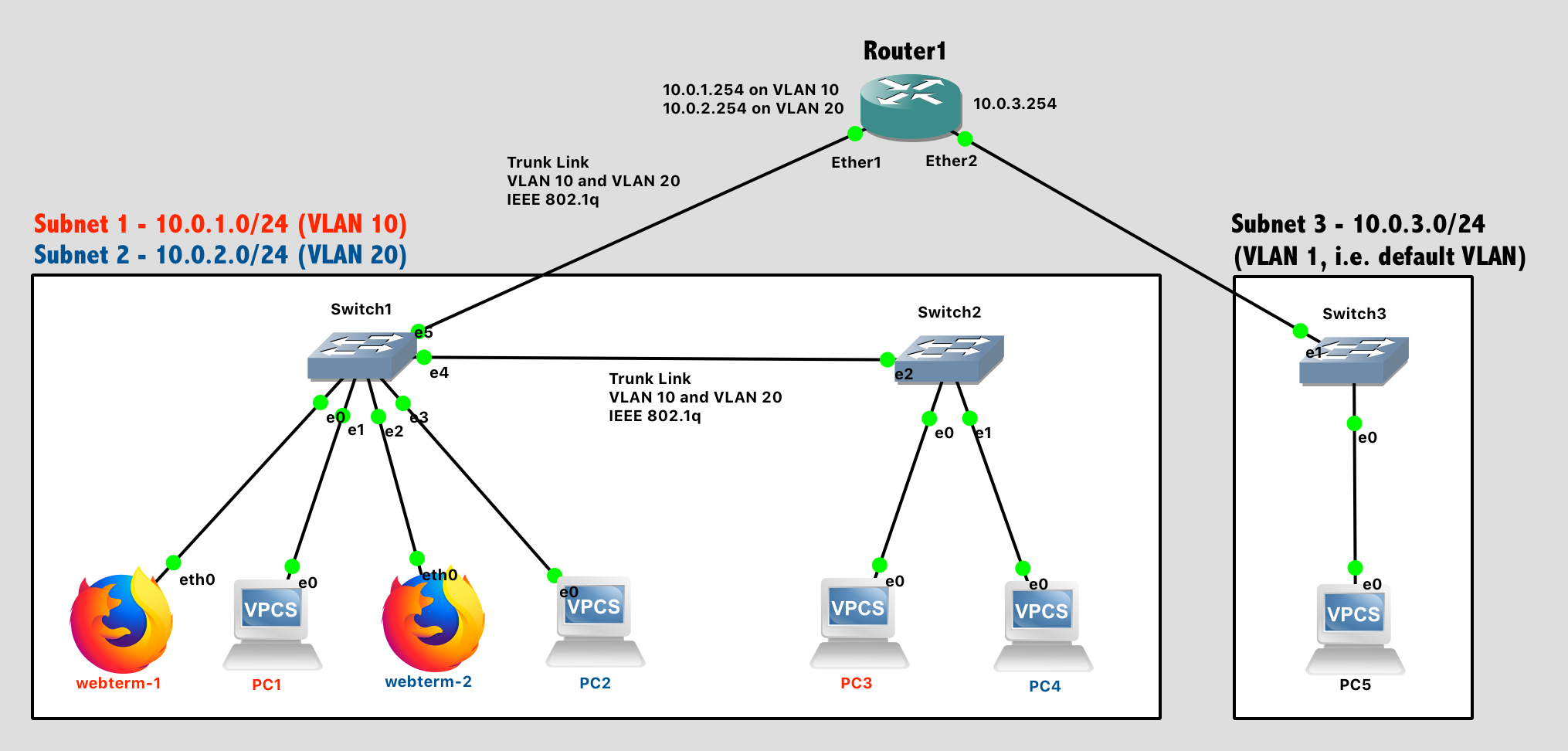
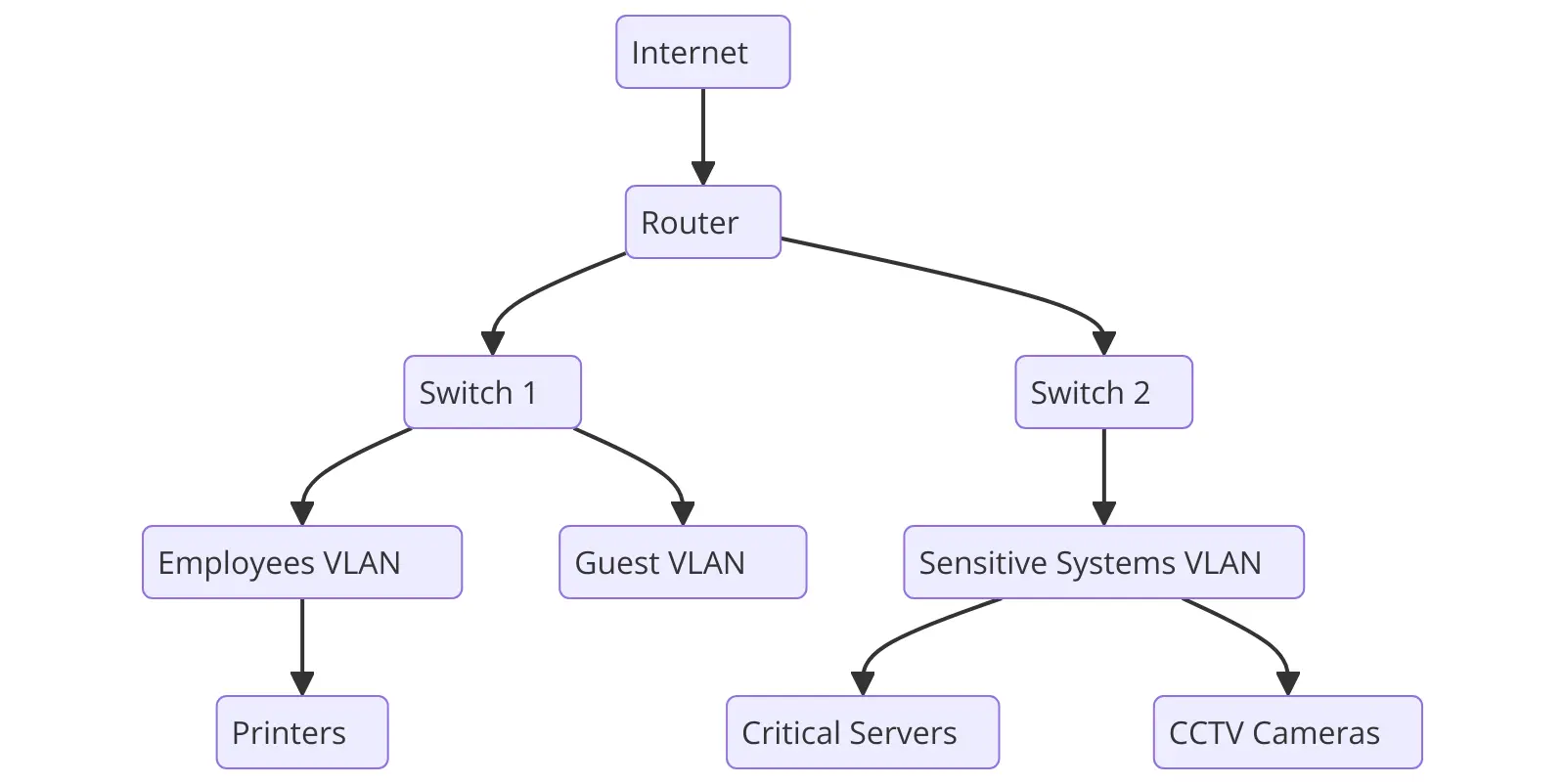
G Network Configuration for Network Segmentation and Isolation involves designing and setting up a network architecture that allows for the division of a single network into smaller, isolated segments. This is achieved through the use of virtual local area networks (VLANs), subnets, firewalls, and zones. The main goal is to create a secure and efficient network by limiting access, containing potential threats, and enhancing performance.Benefits of G Network Configuration for Network Segmentation and Isolation
Implementing G Network Configuration for Network Segmentation and Isolation offers numerous benefits, including: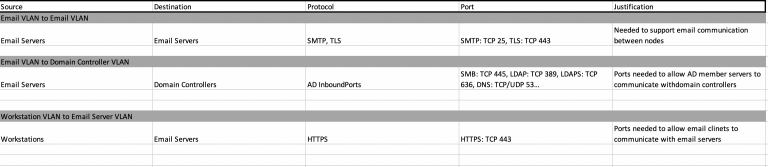
This particular example perfectly highlights why G Network Configuration For Network Segmentation And Isolation is so captivating.
• Enhanced security by limiting the spread of malware and unauthorized access • Improved performance by reducing network congestion • Better compliance with industry regulations by isolating sensitive data • More efficient management by simplifying network monitoring and troubleshootingBest Practices for G Network Configuration for Network Segmentation and Isolation
To effectively implement G Network Configuration for Network Segmentation and Isolation, follow these best practices:1. Determine the Segmentation Strategy