Understanding G Network Security Protocols: Ensuring Secure Communication
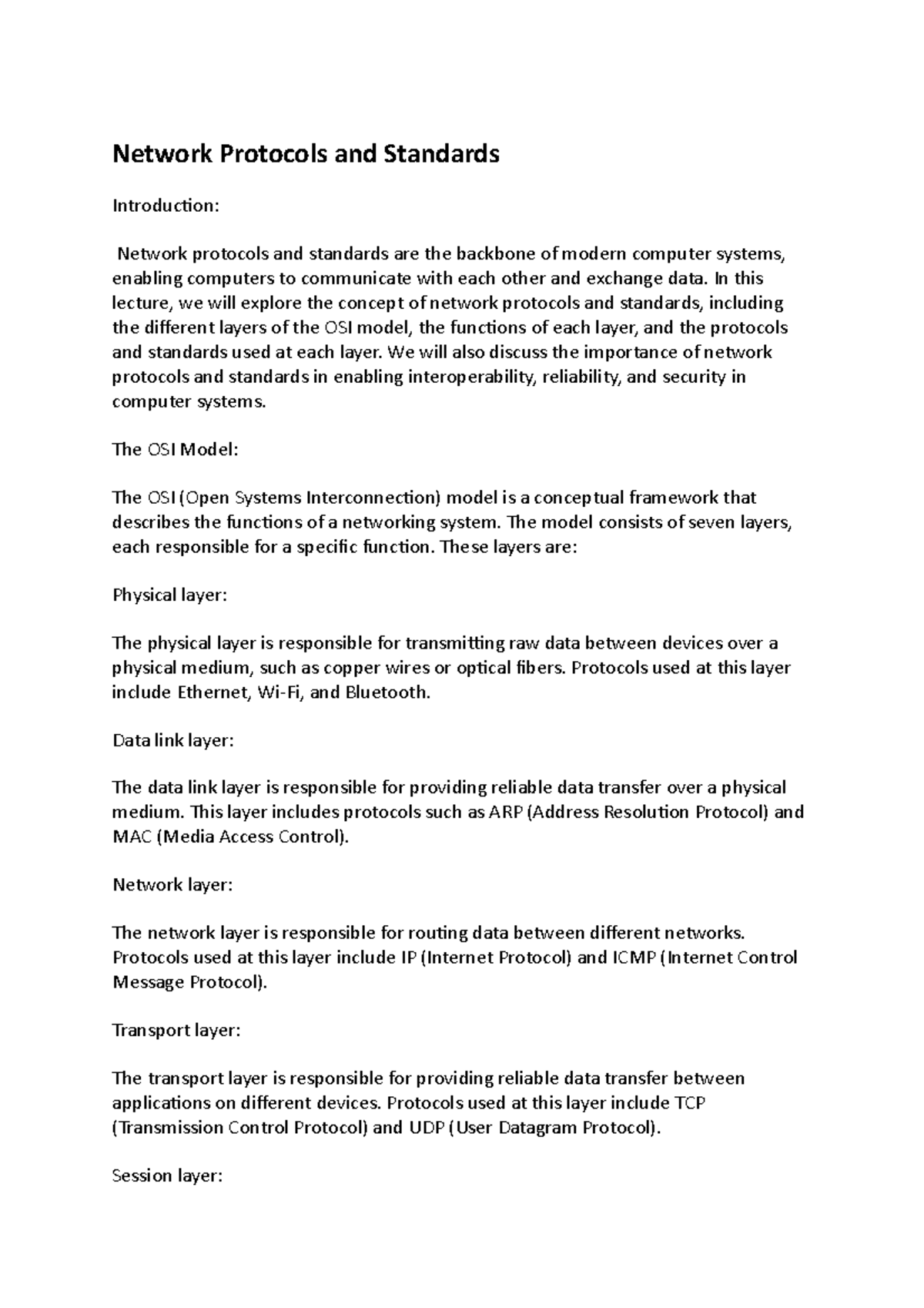
As the world becomes increasingly reliant on digital communication, the need for robust network security protocols has never been more pressing. With the rise of cyber threats, it's essential for organizations to implement effective security measures to protect their data and network infrastructure. In this article, we'll delve into the world of G network security protocols, exploring their significance, types, and best practices for implementation.
What are Network Security Protocols?
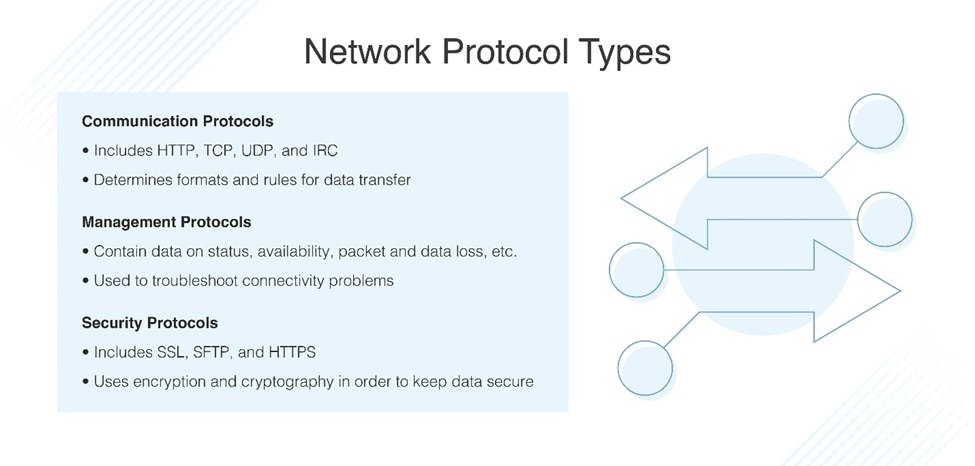
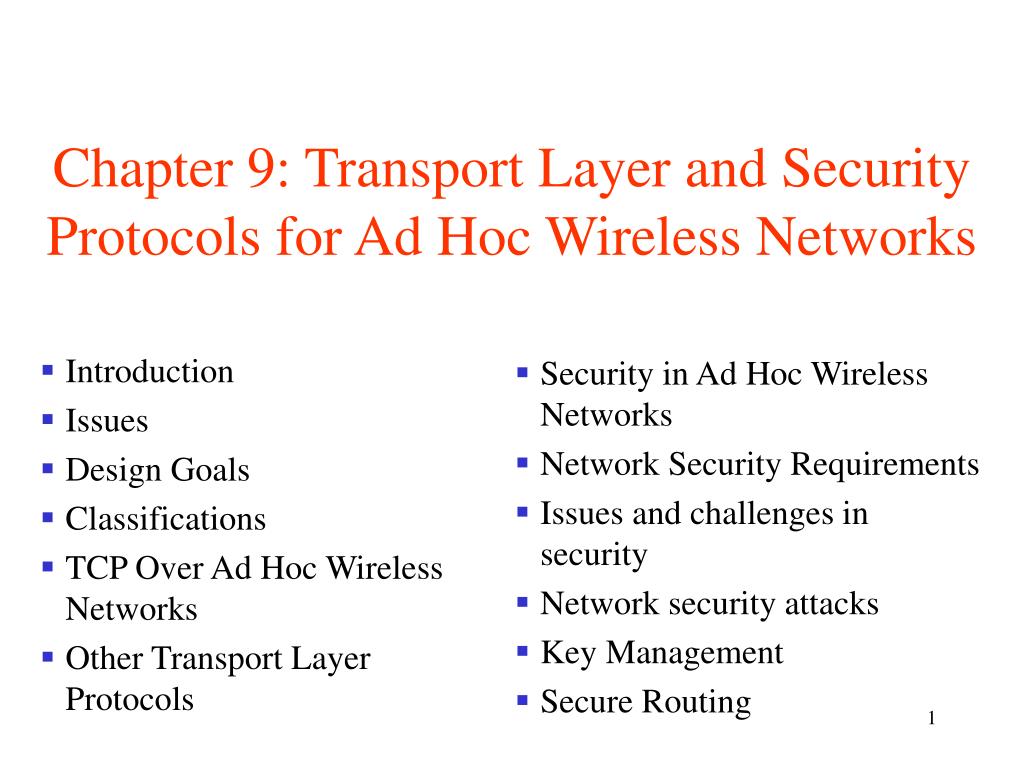
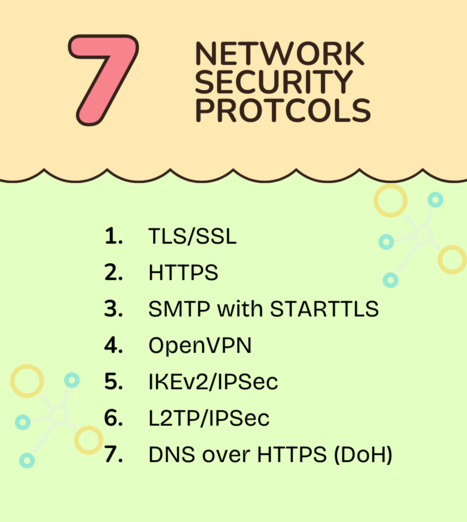
Types of Network Security Protocols

Such details provide a deeper understanding and appreciation for G Network Security Protocols.
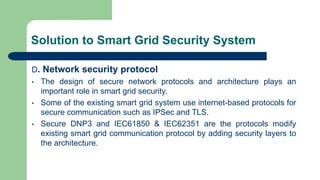
- TLS (Transport Layer Security): A cryptographic protocol used to secure web communications, ensuring data confidentiality, integrity, and authenticity.
- IPSec (Internet Protocol Security): A suite of protocols that provides secure data encryption, authentication, and integrity for IP communications.
- SSH (Secure Shell): A protocol used for secure remote access, allowing users to securely access and manage network devices.
- SSL/TLS (Secure Sockets Layer/Transport Layer Security): A cryptographic protocol used to secure web communications, ensuring data confidentiality, integrity, and authenticity.
- SFTP (Secure File Transfer Protocol): A protocol used for secure file transfer, ensuring data confidentiality, integrity, and authenticity.
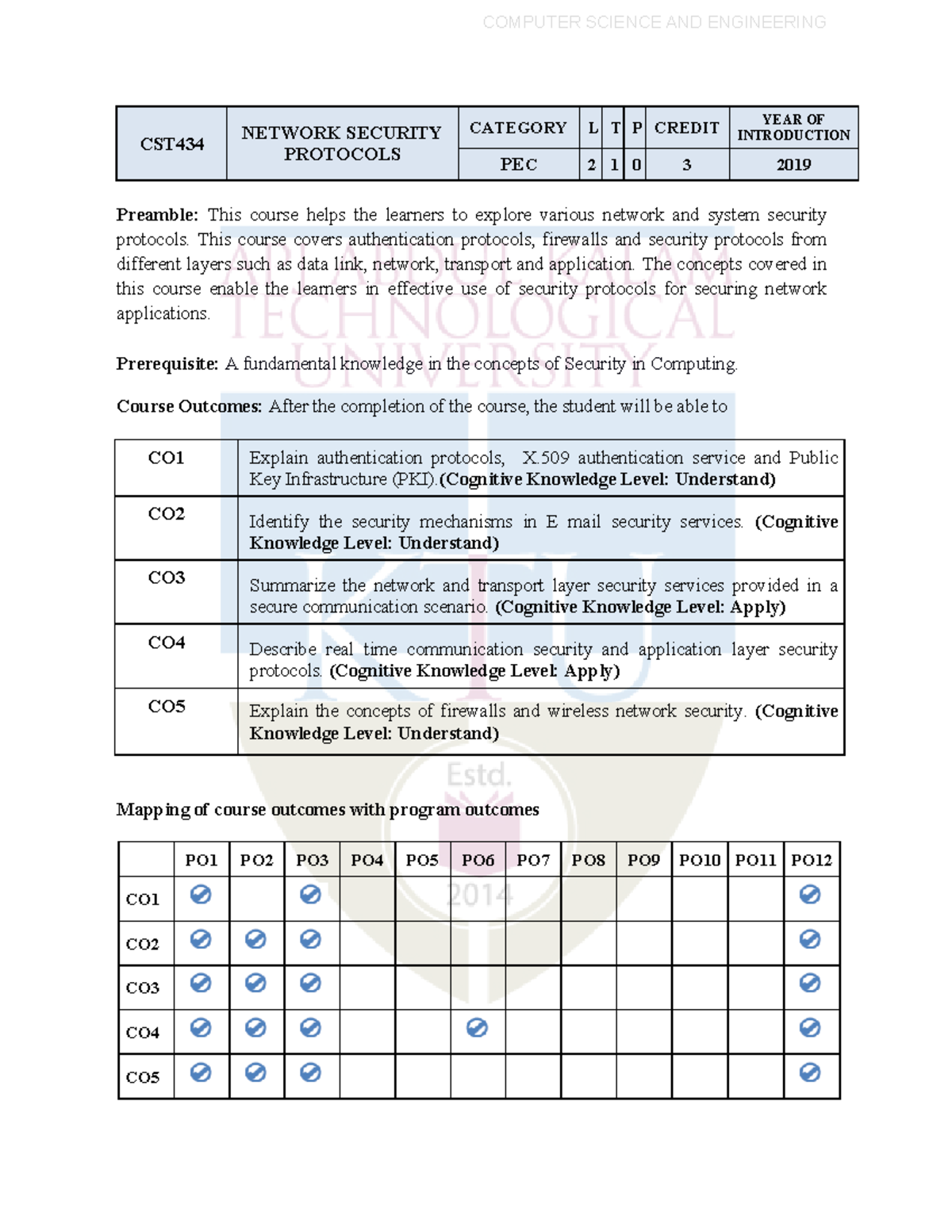
G network security protocols play a vital role in ensuring the confidentiality, integrity, and authenticity of data as it traverses the network. By implementing robust security protocols, organizations can protect their data from cyber threats, prevent unauthorized access, and maintain a secure and reliable network infrastructure. This is particularly crucial for organizations handling sensitive data, such as financial institutions, healthcare providers, and government agencies.
Best Practices for Implementing G Network Security Protocols
Such details provide a deeper understanding and appreciation for G Network Security Protocols.
Implementing effective G network security protocols requires a thorough understanding of the different types of protocols, their strengths, and weaknesses. Here are some best practices for implementing G network security protocols:
- Conduct regular security audits: Regular security audits can help identify vulnerabilities and weaknesses in the network infrastructure, allowing organizations to take corrective action and implement necessary security measures.
- Implement multi-factor authentication: Multi-factor authentication adds an extra layer of security, ensuring that only authorized users have access to network resources.
- Use encryption: Encryption ensures that data is scrambled, making it unreadable to unauthorized parties, even if they manage to intercept it.
- Regularly update software and firmware: Regular updates can help patch vulnerabilities and ensure that software and firmware are up-to-date with the latest security patches.
- Implement firewalls and intrusion detection systems: Firewalls and intrusion detection systems can help prevent unauthorized access and detect potential security threats.
Conclusion

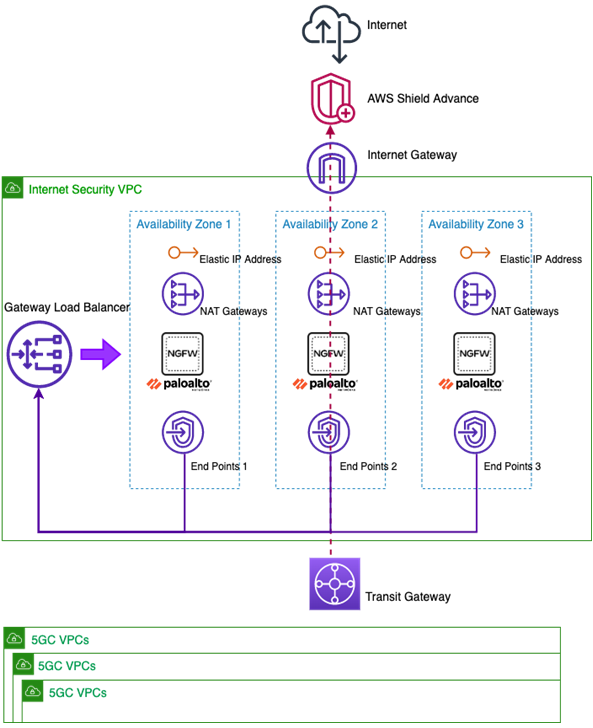
Furthermore, visual representations like the one above help us fully grasp the concept of G Network Security Protocols.
G network security protocols play a vital role in ensuring the confidentiality, integrity, and authenticity of data as it traverses the network. By implementing robust security protocols, organizations can protect their data from cyber threats, prevent unauthorized access, and maintain a secure and reliable network infrastructure. By following the best practices outlined in this article, organizations can ensure that their G network security protocols are effective and provide the necessary level of security to protect their data and network infrastructure.
Recommendations
Based on the information provided in this article, we recommend that organizations implement the following G network security protocols:
- TLS (Transport Layer Security)
- IPSec (Internet Protocol Security)
- SSH (Secure Shell)
- SSL/TLS (Secure Sockets Layer/Transport Layer Security)
- SFTP (Secure File Transfer Protocol)
By implementing these G network security protocols, organizations can ensure that their data is secure, reliable, and protected from cyber threats.






![Network Security Protocols [An Easy-to-Read Guide] Image showcasing Network Security Protocols [An Easy-to-Read Guide]](https://image.slidesharecdn.com/phase2telecommunicationsandnetworksecurityprotocolsimple-221204063954-18c2b99f/75/Phase-2-Telecommunications-and-Network-Security-Protocols-imple-docx-1-2048.jpg)