Ways to Protect Data from Tampering: A Comprehensive Guide
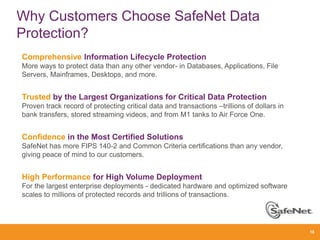
In today's digital landscape, protecting sensitive data has become a top priority for organizations. Data tampering, also known as data manipulation, refers to the intentional modification or manipulation of data without authorization. This can be done through various means, including hacking, malware, or unauthorized access to databases and other data storage systems. To prevent data tampering, it's essential to implement robust security measures that include, but are not limited to, encryption, access controls, monitoring, and employee training.Classify and Enforce Least Privilege

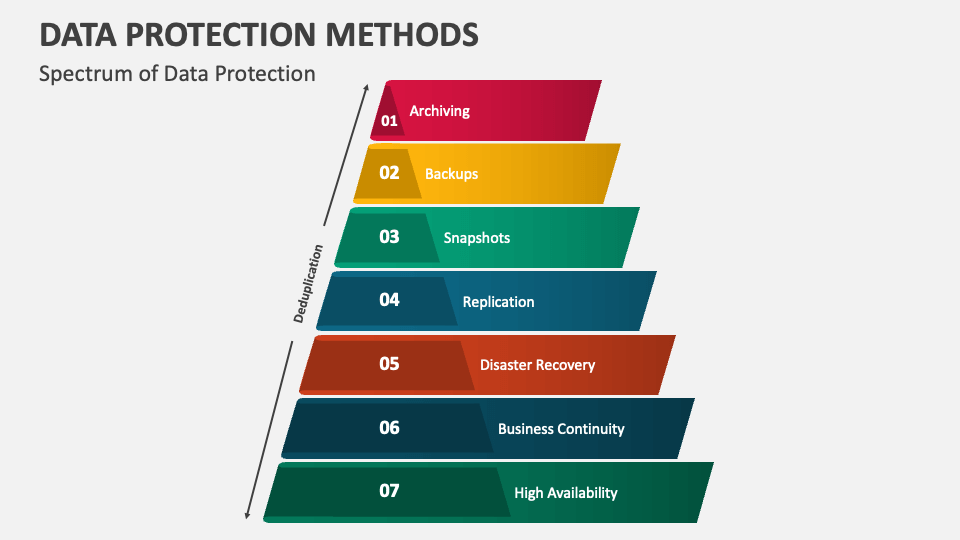
Such details provide a deeper understanding and appreciation for Ways To Protect Data From Tampering.
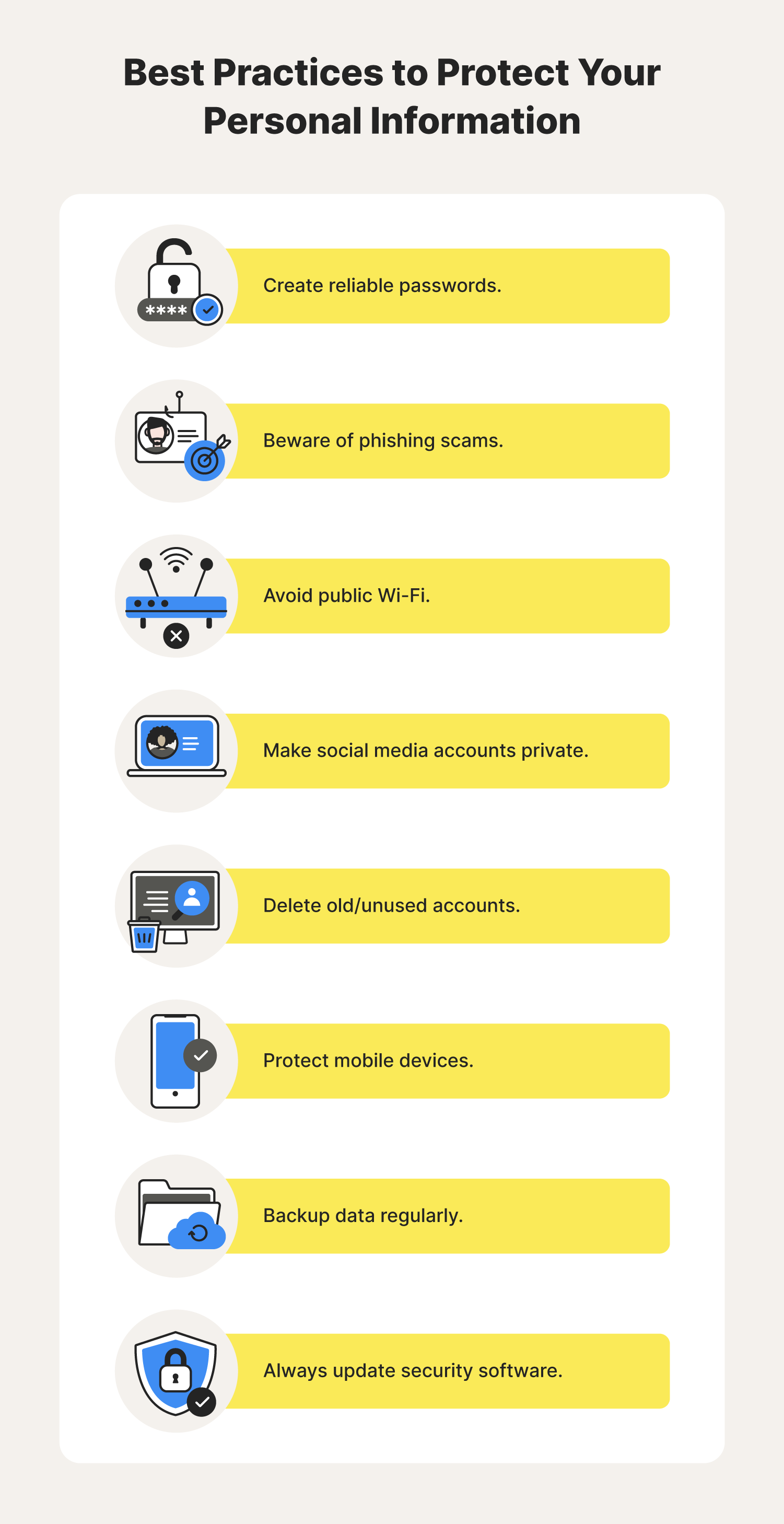
One of the most effective ways to protect data from tampering is to classify sensitive data by its sensitivity level. This involves categorizing data into three levels: high, medium, and low, based on its importance and potential impact on the organization if it falls into the wrong hands. Once classified, enforce least privilege, a security best practice that limits the access rights of users to the minimum necessary to perform their jobs.Secure Data at Rest and in Transit
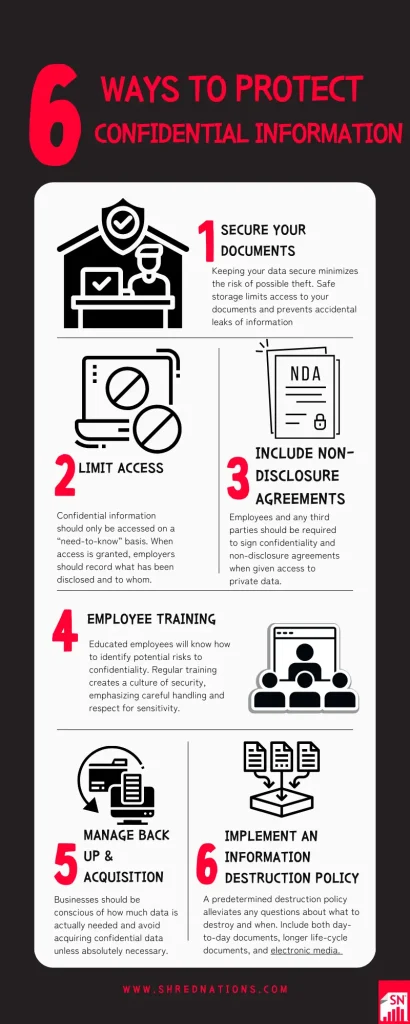
Furthermore, visual representations like the one above help us fully grasp the concept of Ways To Protect Data From Tampering.
Protecting data in transit and at rest is critical in preventing tampering. Use encryption techniques, such as SSL/TLS, to safeguard data when transmitting it over the internet or within the organization. For data at rest, utilize encryption algorithms and secure communication protocols to ensure data confidentiality and integrity.Implement Access Controls and Role-Based Access Control (RBAC)